The American Numismatic Association and Numismatic Guarantee Corporation recently issued press releases notifying the public that there have been attempted phishing scams by trying to impersonate a hotel service or someone who works for NGC. Since this is back in the news, I am taking an article I had previously written on the topic and updating it to be more current.
The American Numismatic Association and Numismatic Guarantee Corporation recently issued press releases notifying the public that there have been attempted phishing scams by trying to impersonate a hotel service or someone who works for NGC. Since this is back in the news, I am taking an article I had previously written on the topic and updating it to be more current.
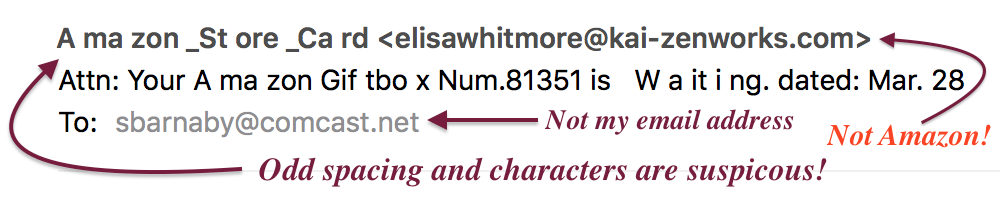
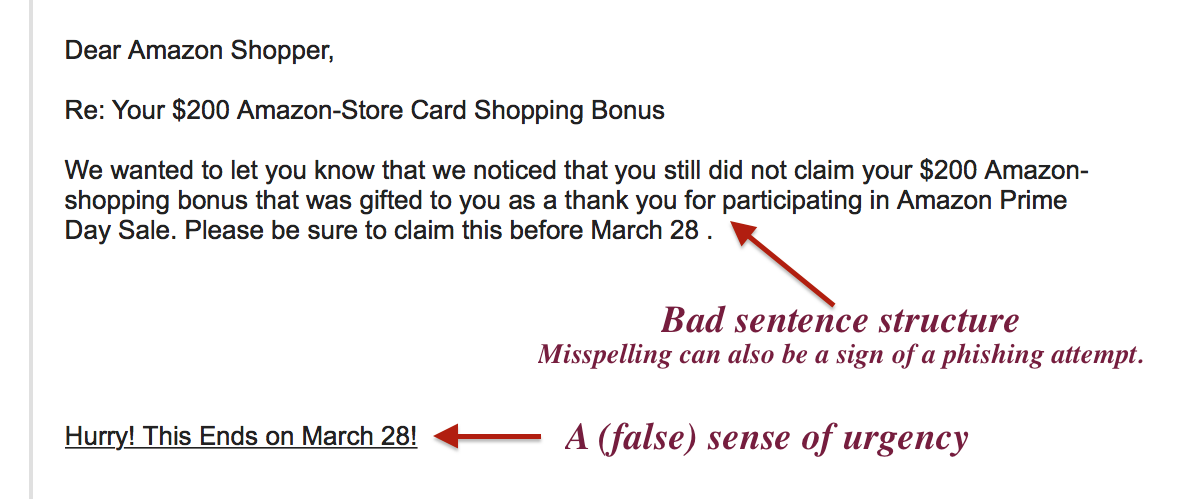
Phishing is the term used to describe the attempt to convince someone to reveal personal information by sending them an email that looks like it came from a legitimate source. Unfortunately, it is so easy to spoof (trick) the Internet’s email system that all it takes is someone with attention to detail to get past spam and other security filters.
Last year, I retired as an information security professional where, for the last 25 years, was contracting to the United States government. I saw many attempted and successful attacks against both government and commercial systems. However, the one attack that is the most difficult to defend is those where humans are convinced to act against their own best interest. The technical industry calls them phishing attack but they are forms of social engineering.
A social engineering attack tries to use something about you or something you care about to convince you to do something that could potentially harm you. For example, an attacker looking to scam someone who collects rare coins may know about NGC’s business. Knowing that the people who might be using NGC’s services are collectors with a lot of disposable income, they could use the weaknesses of the email system in order to fool the recipient into a situation where they can be taken advantage of.
To help you stay safe, the following are rules you can follow to keep safe online:
Rule #1: Unless you are 100-percent certain that the email is legitimate, do not click on the link!
You will be never 100-percent certain that any email you receive is legitimate. Thus, make sure that you are as close as 100-percent certain as possible. One thing you can do is to move your pointer over the link, stop, and wait for the tooltip to show you the address.
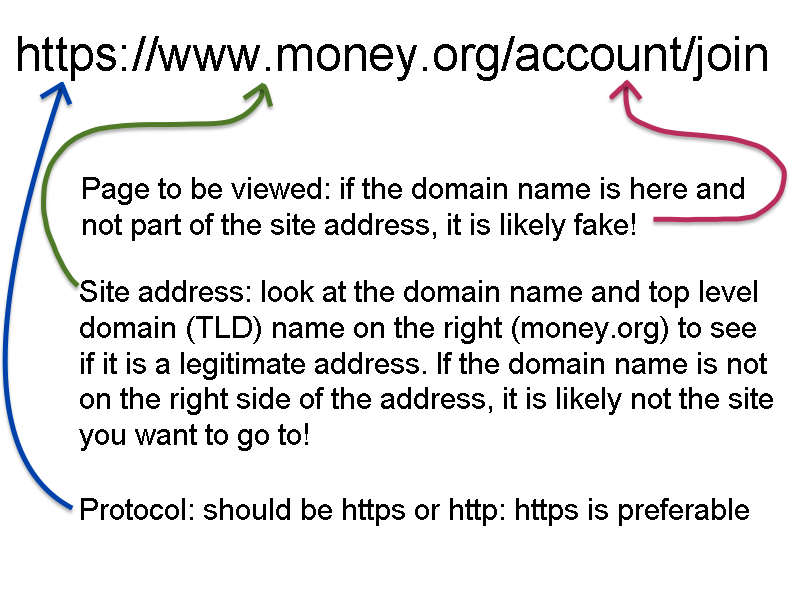
Tooltips are those balloon-like popups that will tell you something about the link or element before you press the mouse button. One way to tell that a link is bad is that if the address is not what you think. For example, if the link is supposed to send you to the ANA website, the tooltip better say that it will send you to money.org. If it does not, then do not click on the link.
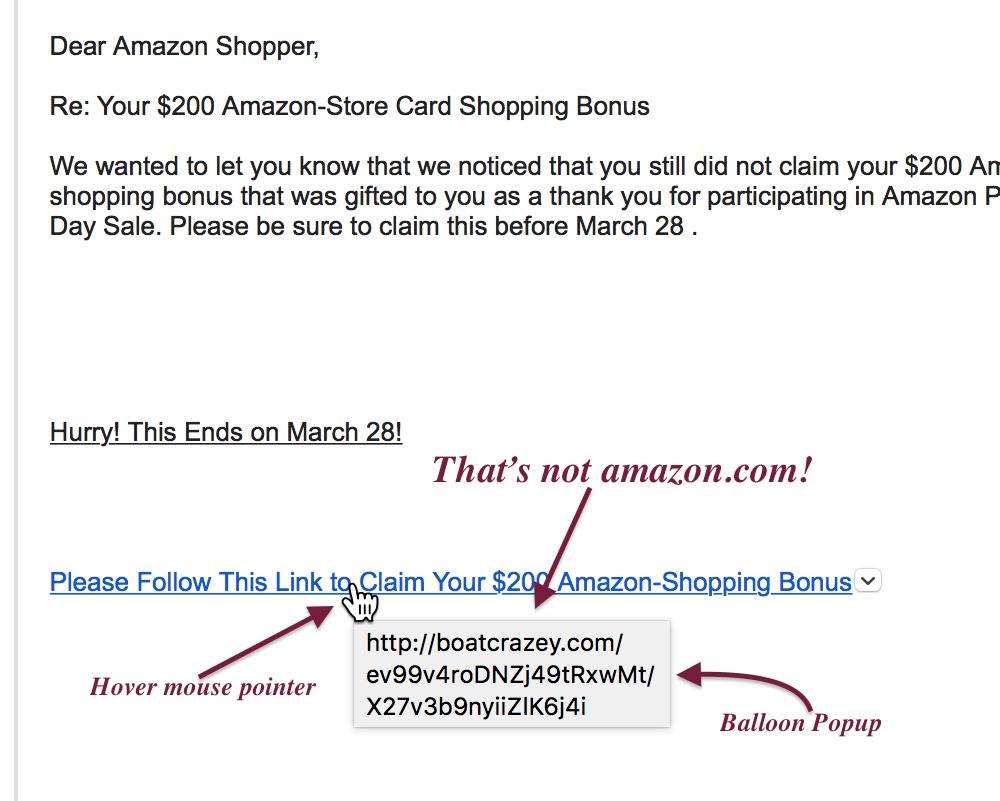
Place your mouse pointer over the link and let the tool tip appear. What does it say?
When you check the link, the address of the server is the first part of the address. If what should be the server name is not in that area at the beginning of the address, do not click on the link.
One trick the phishers use is to show you what looks like a complicated address in the message, but the link behind it will send you to another website. This is where tooltips can help. If you hover over the address and they do not match, it is an attempt to trick you and you should not click on the link.
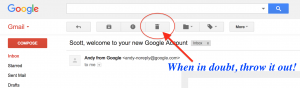
If you are using a web-based email client, such as Gmail, you can check the address on the status line at the bottom of your browser window. Check to see if the address makes sense. For example, if the email claims to be from Amazon, the link should say “amazon.com” and nothing else. Sometimes phishers will try to write a link using something after the address like “amazon.com.anothersite.co” to fool you. Do not be fooled. A link like this is trying to send you to “anothersite.co” and not Amazon.
If you are unsure about the link, then go to your browser and type in the address yourself.
As with everything in life, there is an exception to the rule. Organizations, like the ANA, will use mailing list services to send out notices to members and anyone else who have signed up for these emails. Unfortunately, the URL you will click on will be one associated with the mailing list service. The service uses this to provide engagement statistics to whoever is sending out the email. For example, for the service that the ANA uses all of the links are to r.listpilot.com.
Mailing list services are great resources for many organizations and their tracking service is necessary to understand the effectiveness of the communication. If you are not sure, continue to visit the organization’s site without clicking on the link.

An example of an email message showing what to look for to understand how to identify it as a phishing attempt.
Rule #2: No legitimate company or organization will ask for information to be sent via email
One of the tactics that the phishers use to try to trick you into giving them your personal information is to create a form that looks like it is legitimate. Just as it is easy for someone with moderate skills to fake a web page they can also create a counterfeit form. Not only will the form be counterfeit, but they could also embed programs in that form to steal your information.
Embedded code in documents is called macros. Macros are used to command programs to do something for the user. When used in productive environments, macros can be a wonderful tool to create dynamic documents and provide input validation. But the same instructions that can make macros a productive tool can also be used to do bad things.
Unless you are certain about where the document came from, do not open a document. If you open the document and the program asks if you should enable or run macros, do not enable macros.
This is not just a problem with word processing document. PDF documents can also deliver very nasty malware (malicious software). Not only can an attacker add macros to a PDF document, but someone can embed Flash in those PDF. Flash is the technology that helps you watch online videos and add enhancements to the visual interface of some websites. But Flash can be used to attack your computer system. Opening a PDF file sent by someone you do not know can be as dangerous as a word processing document.
Rule #3: Do not open suspicious attachments
Another trick the attackers try to use is adding an attachment named in a way to entice you to open the file. File names consist of the name of a file followed by a period followed by a file extension. The file extension is used to tell the computer the type of program to execute to allow you to work with the file. There are three file extension that very dangerous and should never be opened unless you are absolutely sure who sent them: .zip, .exe, and .dmg for Mac users.
The .zip file extension tells the computer that the file is something called a Zip archive. A Zip archive is a file that is formatted to allow it to store many files that are compressed. Zip files are used for many legitimate purposes including being the default format of Microsoft Word’s .docx file. Unfortunately, it can contain programs and files that can be used to attack your system.
One of the types of file that can be included in a Zip archive is a .exe or executable file. Simply, these are programs in the same way that Microsoft Word is a program. Once an executable file is opened, it will do whatever it is programmed to do. Among the things that the program can do is keylogging. A keylogger reads what you type on your keyboard, what you click on the screen, and in some cases, what is displayed on your screen. The keylogger will be able to capture the username and password you entered when you visit any website including your bank’s website. The problem is that when a key logging program is run, you do not know it is watching what you type. Nor do you know that it connects to a server somewhere on the Internet to send the information to the attacker. Keyloggers and other malware can infect your system in a way that allows it to continue to exist, even if you reboot the computer.
You may ask about anti-virus software helping stop malware. Anti-virus software is programmed to understand what is known about attack vectors. It cannot protect you if it does not know how the virus works. Remember that the government warned that last year’s flu vaccine was not effective for the version of the virus infecting people? Anti-virus software is similar that if it doesn’t know about the strain it cannot protect you. Hackers are always looking for ways to fool anti-virus software.
For Windows user, you should consider running Windows Defender. Windows Defender is built into Windows but cannot be run if you have another anti-virus software. I use Windows Defender and have been happy with the results. If you want more information about Windows Defender visit this page on Microsoft’s support site.
While Macs are more difficult to attack they are not immune. Mac users should never open a file with a .dmg file extension unless you know who sent the file. The Macintosh .dmg file is a disk image stored as a regular file. A disk image file is formatted to look and acts like a disk so that when you double-click the icon, it will mount on your computer as if you plugged in an external disk drive. Because .dmg files are commonly used to install legitimate software, sometimes the installation can be automatically started. If you allow the installation to continue, you can install software as dangerous as what I described for the Windows .exe file.
OS X is a different type of operating system where if you are careful you can get away without running an anti-virus program. However, if you want to be paranoid (along with me) you might want to run the free anti-malware software from Malware Bytes.
Regardless of the operating system and software you use, ALWAYS KEEP IT UP TO DATE! Patching your computer may be an annoyance but the dangers, if you do not apply security patches, will hurt more and last longer!
Rule #4: When in doubt, throw it out!
 While all this seems simple to me after having worked in this industry for nearly 40 years, I have seen how these concepts are confusing to the non-technical user. The problem with email is that it was developed as a way for researchers to communicate by plain text across Arpanet, the forerunner of the Internet. Email, as a text-based service, \ has been extended in so many ways that it has created a complicated series of standards that require a degree in computer science to analyze. While these complications make it easier to communicate via email it also makes it difficult to secure.
While all this seems simple to me after having worked in this industry for nearly 40 years, I have seen how these concepts are confusing to the non-technical user. The problem with email is that it was developed as a way for researchers to communicate by plain text across Arpanet, the forerunner of the Internet. Email, as a text-based service, \ has been extended in so many ways that it has created a complicated series of standards that require a degree in computer science to analyze. While these complications make it easier to communicate via email it also makes it difficult to secure.
Even if you cannot fully analyze whether the message is spam or legitimate, if you have any doubt, then just press the delete button. If the message came from a source you know, contact them off-line and ask if the mail is legitimate. If you think the email is from your bank, call the bank and ask. If you think the email is from your credit card company but not sure, call the credit card provider and ask. If you think the email sent from the ANA or NGC is suspicious, call them and ask.
A little intuition and some due diligence can be of great help in these circumstances.
Stay safe online!